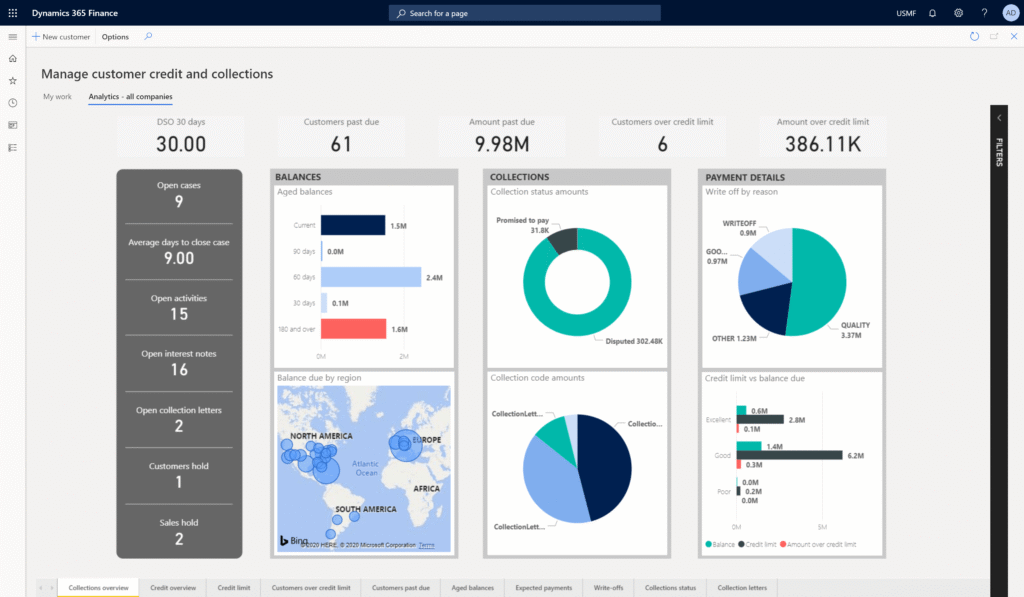
In complex ERP environments, control over user access isn’t just a technical matter it’s a structural requirement. As businesses increasingly depend on platforms like Microsoft Dynamics for finance, operations and compliance, the lack of clarity around permissions becomes a growing concern.
Without proper insight into who can do what, systems may look secure on the surface while hidden risks remain underneath.
Role assignments often go unnoticed
When roles are created at implementation, they often remain unchanged even as teams evolve. Employees switch positions, new modules are added, and external consultants come and go yet permissions are rarely revisited.
Over time, this leads to a cluttered access landscape with overlapping rights and invisible vulnerabilities. Without structured oversight, even routine operations can introduce risk.
A full-cycle view of user access
Some organizations are addressing this issue by implementing continuous permission control across all stages: design, assignment, adjustment, and audit.
2-Controlware supports this model by offering tools that provide ongoing visibility into how authorizations are structured and used within Microsoft Dynamics.
Rather than reacting after something goes wrong, companies gain the ability to proactively manage their internal access landscape.
Hidden risks impact real outcomes
Incorrect or excessive permissions are not just an IT issue they affect real business operations. A user with unintended access could override workflows, alter financial data, or change approval settings without proper oversight.
Even if no harm is intended, the lack of structure creates room for error. In industries where regulatory compliance is strict, these small gaps can quickly become major liabilities.
Audits demand clean documentation
External audits increasingly focus on system access, and vague answers are no longer acceptable. Organizations must be able to show who has access, why they have it, and when it was last reviewed.
Without central control over permissions, producing this documentation can be time-consuming and incomplete. Structuring access through ongoing monitoring simplifies the audit process and reinforces accountability.
Shifting from setup to lifecycle thinking
Access management used to be seen as a project task, something handled during implementation, then forgotten. That mindset is rapidly changing. Today, user roles and permissions are treated as part of day-to-day system health.
Companies that adopt this lifecycle approach are better equipped to respond to change, reduce internal risk and meet compliance expectations without last-minute scrambles.
Control tools become part of business stability
As digital systems become more central to daily work, the tools used to manage them are shifting from optional add-ons to critical infrastructure. Businesses are starting to treat permission control with the same seriousness as data security or financial integrity.
In that context, platforms that make authorization visible and manageable help create the foundation for responsible system use.